Layer 8 Security

By A Mystery Man Writer
Layer 8 Security | 1,985 followers on LinkedIn. Solving data risk management challenges with practical security, compliance, and privacy strategies. | Layer 8 Security is a cybersecurity consulting, advisory, and technical services company that creates risk management solutions for your evolving information security and compliance needs. Today’s business environment requires seamless integration with third-party vendors, clients, and partners. We ensure your information ecosystem is secure, compliant and resilient to the severity and frequency of a disruption resulting from a cyber attack.
Layer 8 Security is a cybersecurity consulting, advisory, and technical services company that creates risk management solutions for your evolving information security and compliance needs. Today’s business environment requires seamless integration with third-party vendors, clients, and partners. We ensure your information ecosystem is secure, compliant and resilient to the severity and frequency of a disruption resulting from a cyber attack.
The Layer 8 Security philosophy is focused on the human layer of cybersecurity. where business processes and technology intersect. As the cyber threats evolve in sophistication so must the defenses of companies, starting with its people. We are passionate about what we do. We refer to ourselves as Sheep Dogs; we feel a benevolent call to help others.

emt Distribution signs Layer 8 Security to address the human dimension of cyber risk prevention - emt Distribution Pty Ltd

Hack the Stack: Using Snort and Ethereal to Master The 8 Layers of An Insecure Network by Stephen Watkins, George Mays, Ronald M. Bandes, Brandon Franklin, 9781597491099, Paperback

Why Layer 8 Security Serves Biotech and Life Sciences Companies

Layer 8 Security

Layer 8 Security establishes scholarship for info science students

Future of IoT with 5G Technology
Layer 8

Layer 8 Security

Layer 8 Security (@layer8security) / X

ASHRAE

EMT Distribution adds Aussie security training vendor Layer 8

Layer 8 Security (Australia) Company Profile: Valuation, Investors, Acquisition 2024

Layer 8 Security CEO to give Great Valley commencement address
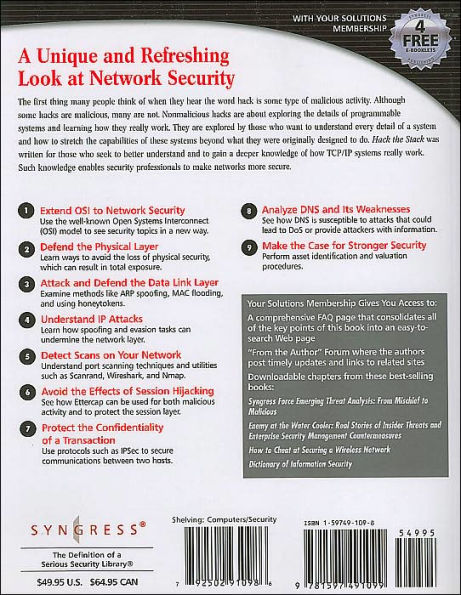
Hack the Stack: Using Snort and Ethereal to Master The 8 Layers of An Insecure Network by Stephen Watkins, George Mays, Ronald M. Bandes, Brandon Franklin, 9781597491099, Paperback

A Pedagogic Cybersecurity Framework – Communications of the ACM
- Specialist For Layer 8 Problems Poster for Sale by shop-dk

- Layer 8 - Soluções em Conectividade - Consultoria e Serviços de
- Top Quality 8 Layer PCB Stackup Manufacturer and Supplier

- 8-Layer PCB Stack-up: Maximizing Electronic Performance - MorePCB

- Stackup for 4, 6, 8,, 18 layers Multi-layer laminated structure

- Compression Thigh Sleeve Leg Pain Relief Wrap Hamstring Brace Support Men Women

- DEDICATED - Soft Cap Seersucker Cashmere Pink

- Adhesive Push Up Bra Pads, Bra Pads Inserts, Push Up Sticky Bra

- Strapless Push Up Bra Women Front Closure Seamless invisible Lingerie Bralette

- Innovative precast reinforced-concrete hollow-core slab system changes Central Asian cities - Concrete Plant Precast Technology

